n this VMware ransomware breakdown we are going to take a closer look at Cheerscrypt. A very special thank you to our friends at TrendMicro for their great breakdown on Cheerscrypt. Now, let’s take a closer look at what makes this one a little different from the rest.
Cheerscrypt Ransomware Targets VMware ESXi
Cheerscrypt is an interesting one because it is a Linux based ransomware, without a Windows counterpart, while many other malicious actors run with both Linux and Windows versions.
It also follows the popular double extortion scheme that many ransomware groups are using lately. Why, it is simple. The double extortion method consists of both of encrypting files as well as exfiltrating data. This is because threat actors are driven by monetary gain and want to make sure victims pay the ransom.
Here’s where things start to get really, really interesting. TrendMicro noted that Cheerscrypt is based on the Babuk ransnomware which was leaked in 2021. Babuk ransomware was multiplatform ransomware had versions that targeted Windows, ESXi, and NAS. This is a really interesting discovery because many ransomware families do have similarities between them.
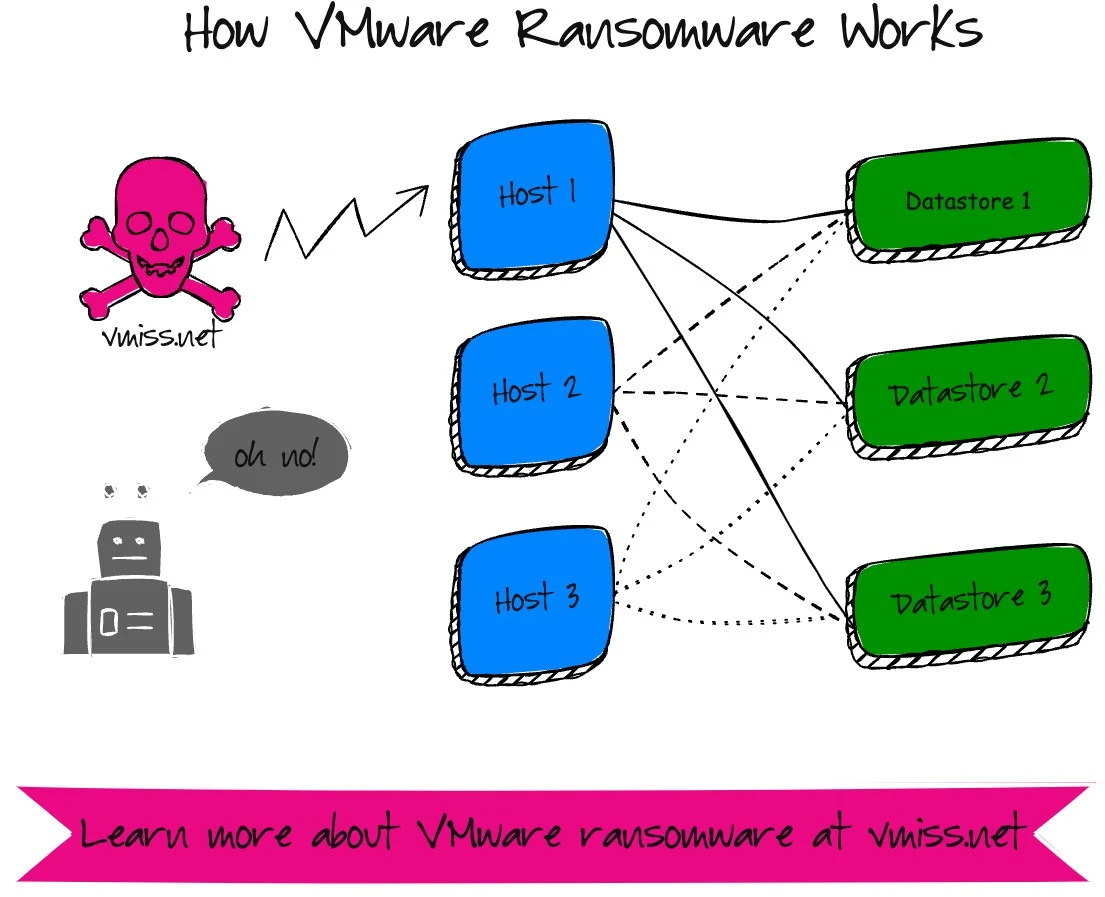
VMware environments are interesting, because there are really a few different attack surfaces to think about. We have the virtual machines, which is what everyone usually focuses on, but we also have the vSphere layer too – vCenter which is the management system for the ESXi hypervisor hosts, and the ESXi hosts themselves.
VMware environments are a popular target, because there is a massive amount of damage that can be done in a relatively short time period.
How Cheerscrypt Encrypts Virtual Machines
It is important to remember fundamentally how a virtual machine is stored on an ESXi server. Remember, a virtual machine is nothing but a collection of files living on a storage volume. Virtual disks are simply files, nothing more.
Cheerscrypt first shuts down the virtual machines, then encrypts them. This is because the files that ransomware targets are locked while a VM is running, which means they cannot be encrypted as long as the VM is powered on. As a bonus, the VMware ESXi host then has extra power to encrypt these files, since now CPU cycles are not being used by virtual machines.
From there, each ransomware strain usually has a slight twist on what type of encryption they use and what processes they follow. For example, Cheerscrypt renames the files before encrypting them and adding the .Cheers extension. While the source code looks very very similar, Babuk encrypted the files before renaming them.
How ESXi Hosts Get Compromised
To execute the encryption commands, an attacker must have access to the ESXi shell, which is accessible via SSH. It is IMPERATIVE that SSH IS DISABLED for ESXi hosts. The reason that the ESXi shell feels so much like Linux, and the reason why these Linux ransomware strains work is due to the inclusion of BusyBox in ESXi for management purposes. VMware is NOT Linux.
While you’re at it, go ahead and disable the ESXi shell too.
There are many ways for an attacker to gain this access. By disabling ssh, one of the most common methods of attack can be disabled. There are published threat actor playbooks that talk about all of the way to compromise ESXi servers, which I will not be going into detail on.
I will say that it is essential to check out VMware’s ransomware resources, especially the hardening guide for suggestions on how to defend ESXi from ransomware attacks.
Remmeber, threat actors will actively try to compromise your VMware environment, because they know that it is a quick way to cause a lot of damage, and hopefully get you to pay the ransom. After VMware is compromised, I firmly believe that it should be nuked from orbit, and organizations should start over. It is not about recovering the VMware environment itself from a ransomware attack, it is about
The virtual machines themselves? Those can be easily recovered from backup, providing they have been protected properly in the first place. This includes making sure the backup repository cannot be compromised by hackers as well. Unfortunately, many cybersecurity strategies do not address the VMware components of an environment specifically, and only focus on the virtual machine layer.
It is important to remember virtualized environments are a huge target, and all components must be included in a cybersecurity strategy. Ransomware gangs are looking to cause damage to the underlying businesses, and destroying the VMware environment is a quick way to accomplish that.
Solid cybersecurity defenses are important for all areas of your infrastructure, but especially critical infrastructure services, which is where VMware belongs.
Want to learn more about VMware ransomware variants? Check out some of my other resources:
f you don’t have an incident response plan specifically for your VMware environment, or you aren’t sure about the security configuration, NOW is the time to act. Remember, it isn’t if you are attacked, it is when. VMware environments are becoming an increasingly popular choice for hackers to attack. A little work now can go a long way later during a ransomware attack.

Melissa is an Independent Technology Analyst & Content Creator, focused on IT infrastructure and information security. She is a VMware Certified Design Expert (VCDX-236) and has spent her career focused on the full IT infrastructure stack.
