One of the most common misconceptions organizations succumb to when moving to the cloud is the cloud is inherently secure. This couldn’t be farther from the truth and many organizations end up with more risk than they bargained for. The worst part? Because organizations often leverage multiple cloud providers, they don’t have a handle on where the risk falls in each of their cloud environments.
It can be difficult to get a handle on configuration management as cloud migrations occur and even more difficult to do it with security in mind. Luckily, Chef Cloud Security makes it simple for organizations to do both.
All About Chef Cloud Security
Chef Cloud Security is the next generation tool for cloud security management. It provides a simple to use unified platform for organizations to use across their environments.
One area Chef Cloud Security really shines in is Cloud Security Posture Management (CSPM).
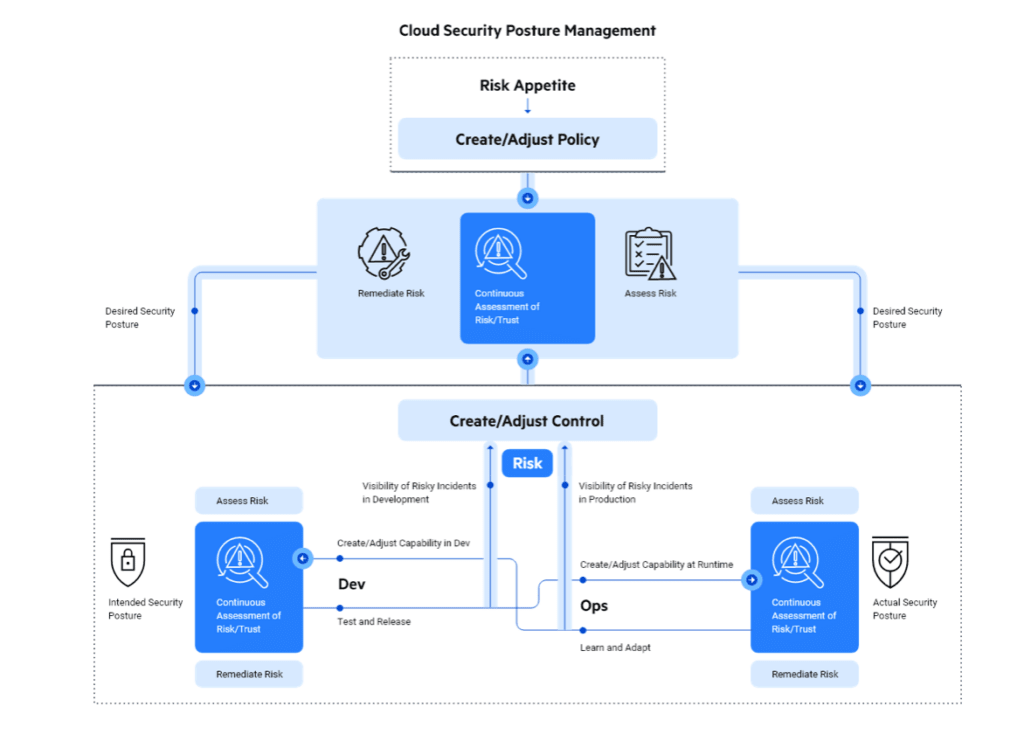
When it comes to securing our environment’s risk is the metric that is top of mind. Chef Cloud Security is continuously auditing cloud accounts and services for security risks and misconfigurations and will help ensure consistent security practices across the major cloud providers.
One of security’s good friends is compliance, and Chef can also audit HIPPA, SOC2, and PCI DSS compliance, which is a consideration for many organizations who are deployed in the cloud (and often something that is a struggle).
This allows organizations to manage their cloud security practices from a single interface instead of relying on point solutions for each area they are deployed in. Chef’s Policy as Code approach merges infrastructure, security, and compliance into a single framework to streamline security operations.
No matter how an organization is deployed in the cloud, Chef Cloud Security can be used to help keep the deployment secure. There is a huge focus on container and Kubernetes security, but more importantly, keeping an eye on the posture from the build to the deployment stages of the app’s lifecycle with a complete history of scan results, policy changes, and control failures.
Chef Cloud Security will also keep an eye on Linux and Windows based cloud instances to help secure them, no matter which cloud they are deployed in. The ability to report on each of the cloud providers in one place is huge, especially when it comes to compliance. Compliance status can easily be viewed on a centralized dashboard and repots can be generated in a single click.
The Problem with Cloud Security
I have found cloud security to be one of the most overlooked and dangerous areas by many organizations. One of the reasons for this can be improper tooling, but many organizations find themselves quickly overwhelmed at the speed of their cloud migrations or deployments.
This is compounded by the fact that many organizations are on a multi-cloud journey to meet their organizations requirements, however they lack centralized monitoring across the multiple clouds they are working with. While organizations should absolutely have a fundamental understanding of the security architecture in each cloud they use, it is easy to spend too much time trying to ensure consistency in security policy across them.
Chef Cloud Security is packed with features to help organizations with this problem, especially since it operates at every part of the development journey. For example, Terraform templates can be checked for security issues before applications are deployed. Could remediation slow the deployment time? It could, however Chef is there to guide you along the path to remediation, and risk in your environment has been dramatically reduced. As part of a future update, Chef will also perform auto-remediation actions to keep the security posture of your cloud infrastructure in line with standard security benchmarks.
To learn more about Chef Cloud Security you can see the product page and request a demo here.
While the opinions stated in this article are my own, this content was sponsored.

Melissa is an Independent Technology Analyst & Content Creator, focused on IT infrastructure and information security. She is a VMware Certified Design Expert (VCDX-236) and has spent her career focused on the full IT infrastructure stack.
